Data Protection
All data information transferred from our website are throughly encrypted and there are no loop holes in transferring or or distributing any business communications received from our stake holders/businness partners. The customer information received through our IT PRO website strictly adheres to our internal compliance and FIM policy.
We at IT PRO always ensure to give you the sufficient online privacy when it comes to communication with our internal teams as the priviacy policy plays a huge role in every step of IT PRO’s success.
Use of Customer Information:
Personal information such as first name, last name, price quote, address will all be archived in our restricted servers when any clients communicates through our website portal.
The use of information may be transferred and followed up only after your approval when two or three vendors we’d like to take on any specific projects. We believe in a broad communication approach before the firm takes to amend any compliance policy.
Disclosure of information:
The information which is passed through IT PRO by means of setting up a product/idea/suggestion will be updated in our Non-discloure agreement.
This process is followed to ensure we have sufficient compliance policies, FIM for the organisation where IT PRO does not involve in any illegal data submission or providing client product portfolio or sugeestions to third party vendors. Exceptional cases, the data submission will takes place when IT PRO is enforcement against any government laws.
Cookies
IT PRO website may use cookies to assist the data we send to your browser and to produce our user statistics report.
The use of this is to understand within IT PRO perspective all the pages our user’svisit and promote enchancing the content and revamp, build a user-friendly site.
How ever you can always disable your cookies on your device by changing the settings of your browser.
Our Featured Services
We are working in IT services for 10+ years and developing software applications and mobile apps for clients all over the world.

Technology Consulting
From helping you to keep up with the latest trends, to understanding the gaps in your application; ST consultants will partner with you to make sure you have every tool at your disposal to get things done right.

Custom Development
ST will build a team of qualified software professionals who will get your project done on-time, on budget and beyond your expectation. We have all the qualified technology professionals to get the project done.

Staff Augmentation
Scale up and down with your staff needs with highly skilled and experienced software professionals who can start on your project right away. We can also help with your contract-to-hire or direct hire needs.
We’ve been triumphing all these 10+ years.
Our IT consulting advisors study your existing software solutions and the ways in which your employees use them, identifying problems in workflows and automation. The advisors design a roadmap and strategy that will help your business leverage the latest technologies and de-clutter your software infrastructure.


How Swyft-Tech assist your business
Bring to the table win-win survival strategies to ensure dotted proactive domination. At the end of the day, on going forward, anew normal that has evolved from the generation on streamlined.
Discussion
Discussion with our experienced IT consultants and IT managers.
Ideas & Concepts
Our IT consultant will listen to your ideas and concepts and provide best solutions.
Quote
Based on the requirements we provide great and reasonable price in the market.
Execute & install
Our Developers and Managers will implement and provide best solutions.
Preparing for your success, we provide IT solutions

IT Management
IT management focuses on how to make information systems operate efficiently. Just as important, it's about helping people work better.

Infrastructure Plan
We involve in the concept of a system approach to installation, operation and management.

IT Consulting
We provide advisory services that help clients assess different technology strategies and, in doing so, align their technology & business strategies.

IT Design
We iterative process of IT design insights: exploration, creation, reflection and implementation.

Data Security
Process of safeguarding digital information throughout its entire life cycle to protect it from corruption, theft, or unauthorized access.

Software Engineering
We deals with the design, development, testing, and maintenance of applications.
Read our latest tips & tricks
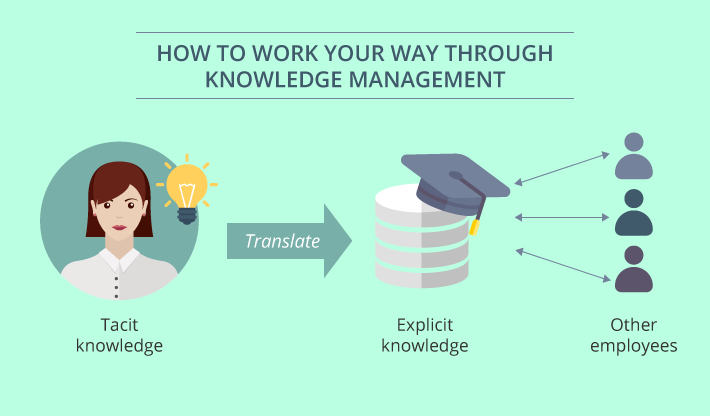
How to work your way through knowledge management
Knowledge is considered the most important asset that organizations...
eSourcing Software: Unlock the Best-Value Deals
eSourcing software equips procurement teams with digital tools to...
IT strategy challenges of a growing business
A growing business is undoubtedly a great joy for...